Introduction
In an era where cybersecurity and national defense are increasingly intertwined, recent revelations about Microsoft’s cloud service practices have reignited critical discussions around data sovereignty and global tech partnerships. Following a detailed report by ProPublica, it was revealed that Microsoft had employed engineers based in China to support Department of Defense (DoD) cloud computing systems—raising significant red flags among government and tech stakeholders alike.
Background: Security Concerns in Government Cloud Infrastructure
Cloud infrastructure is the backbone of modern defense systems, making the integrity of its maintenance teams a national security priority. Government cloud contracts often require strict compliance with data handling and personnel clearance protocols. Any breach in these protocols—even unintentionally—can pose potential vulnerabilities to highly sensitive information.
The ProPublica Report: What Was Revealed
The ProPublica investigation highlighted a system where China-based Microsoft engineers were remotely involved in maintaining DoD cloud platforms. While they were reportedly monitored by “digital escorts”—U.S. citizens with security clearances—these escorts sometimes lacked the technical expertise necessary to fully supervise foreign engineers’ activities, raising concerns about oversight efficacy.
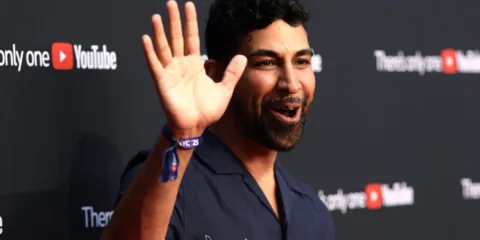
Microsoft’s Response and Policy Changes
In response to growing public scrutiny, including statements from high-level officials like Secretary of Defense Pete Hegseth, Microsoft swiftly issued a statement via its Chief Communications Officer, Frank X. Shaw. The company assured that it has restructured its government support model, ensuring no China-based engineering teams are involved in any capacity with DoD-related cloud services moving forward.
This decisive move is intended to reaffirm Microsoft’s commitment to national security and to maintaining trust with its government clients.
Implications for National Security and Tech Providers
This incident serves as a cautionary tale for all technology vendors working with government entities. It underscores the importance of clear boundaries in global outsourcing, especially when it comes to critical infrastructure. Companies need robust internal compliance mechanisms to avoid missteps that could compromise sensitive data or breach federal regulations.
As cyber threats become more sophisticated, both public and private organizations must prioritize security-driven architectures and transparent operational policies.
The Role of Trenzest in Secure Cloud Solutions
At Trenzest, we understand the growing need for cloud strategies that align with both operational efficiency and national security standards. Our platform is built to support enterprise-grade cloud architecture while ensuring data integrity, access control, and regulatory compliance—particularly for sectors like defense, healthcare, and finance.
Conclusion: Navigating Trust in a Globalized Tech Ecosystem
The Microsoft incident highlights a larger conversation about global workforce distribution, technological sovereignty, and cybersecurity risks. As enterprises increasingly rely on international talent pools and hybrid cloud environments, vigilance and transparency must be embedded in every layer of infrastructure governance.
Platforms like Trenzest are positioned to lead this charge, offering both innovation and integrity to future-ready organizations.